Usable Encryption
Previously
- What is usable?
- What methods can we use to understand usability?
Today
- Usable encryption
UX research methods recap
- Observations
- Interviews
- Surveys
- User studies
- Telemetry
- Diary studies
- Participatory design
- Focus groups
- Experiments
- Cognitive walkthrough
Case study: usable encryption
The paper
Background: encryption
Symmetric vs asymmetric (public key)
Public key encryption basics
Why do we need public-key encryption?
- ✐
What is PGP?
Encryption/decryption software (mostly for emails)
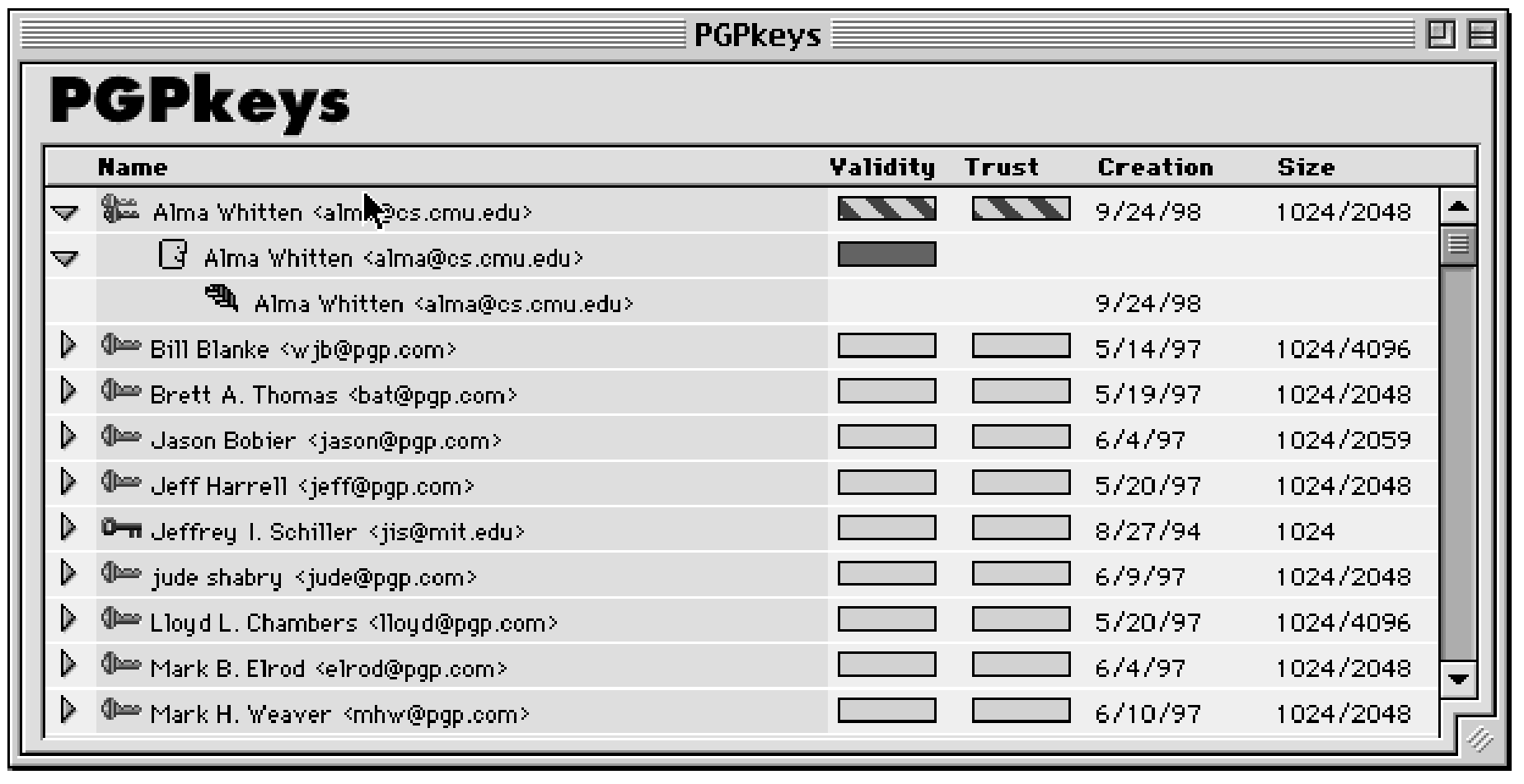
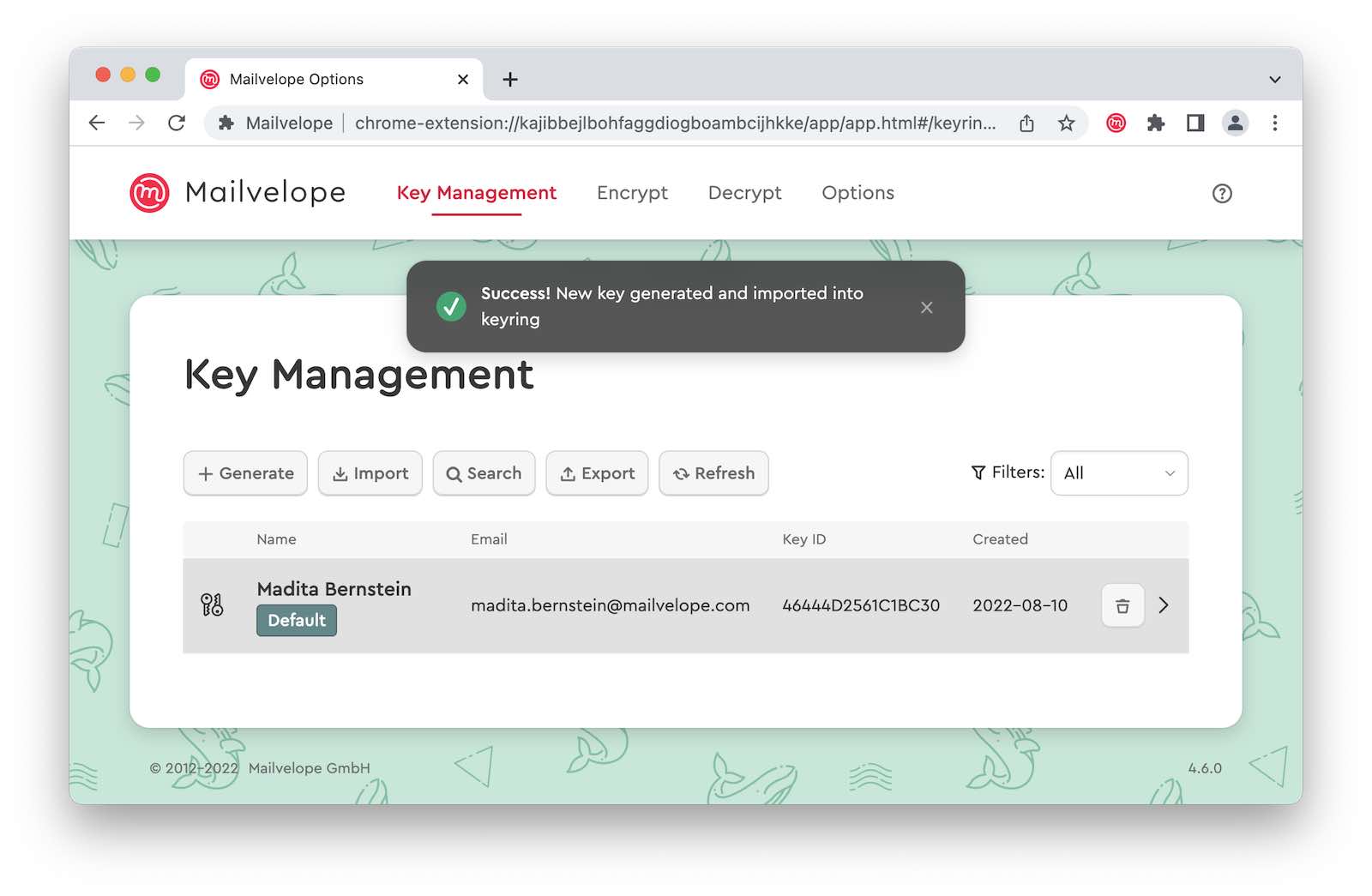
What does it look like today?
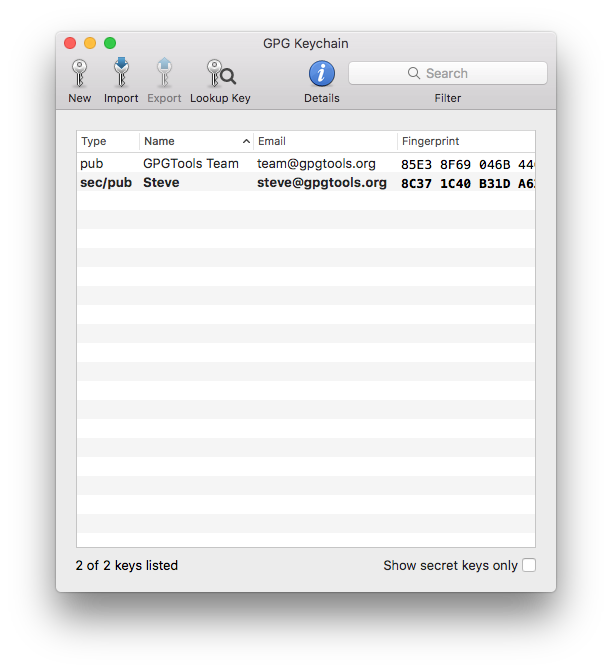
Or maybe this